Yesterday we saw an ESP Host PS4 Payloads Guide, and today mallrats let us know of a recent project of his (aka Treyjazz) dubbed ESPS4ExploitServer- a PS4 Exploit Server for ESP8266 Arduino boards. 
Download: PS4Exploit.zip / GIT / ESPS4ExploitServer fork by 5u770n
To quote from the README.md: ESPS4ExploitServer
This is a project for ESP8266 Arduino boards. It has been tested on a (cloned?) Wemos D1 board with 4MByte flash. It uses SPIFFS to load files from the flash chip but can easily be ported to use an SD addon board.
Setting up the board:
Usage:
It defaults to creating an access point 'ps4exploit' with password 'hackmyps4'. Set your PS4 gateway and DNS to 10.13.37.1 when the board is in AP mode. To change the configuration open a web browser to http://10.13.37.1/settings.
Note that it is an unsecured webpage so the password for a wifi network that is entered in will be saved in plain text, but will only be accessible to those that can log onto the network already. In station mode, the IP for the board will attempt to use the default static IP containing '235'. Ex: 192.168.1.1 with subnet mask 255.255.255.0 will try the static IP of 192.168.1.235
Settings:
Selection of wifi mode - AP/Station AP - Network name, password Station - Available networks, password, static IP Payload - Selection of available payloads loaded in flash
Operation:
It creates a web server and fake DNS server that resolves everything back to itself. It defaults back to sending the index.html on any request that doesn't match a file loaded into flash. SPIFFS doesn't allow for directories so the names of the different exploit pages and scripts (and references in their htmls) had to be renamed. Keep this in mind when adding new exploit pages.
If other payload exploit pages are released you must add some code to set JS_MAX to the number of .js files loaded by the page to trigger the automatic payload setting. After the IDC or Specter exploit pages are loaded through a web browser (or user manual on PS4), the payload transfer will automatically start after a 1s wait. If it fails with a not enough memory error then it is best to restart the PS4 because it typically causes a soft-lock on the XMB after repeated attempts.
Failsafes (useful for when you can't reprogram the board): Programmatically - If the board can connect to a wifi station then it will revert back to AP mode If the static IP you select conflicts with the network you connect to then the network will assign one Physically - Bridging D6 to GND while plugging the board into a power source will force it to load up the default AP settings so you can change the network settings (http://10.13.37.1/settings)
Known bugs: The LED doesn't turn on steady after files are transferred (I think the problem is somewhere in the ESP8266 library) Sometimes after a failed payload transfer the board will be stuck in a loop and need to be reset if you can't connect.
Download: ESP8266 ESP32 HTTP OTA server / GIT
Download: Ps4Exploit-455-By-Draqen-v1.2 for esp8266EX.bin (4.0 MB) / nodemcu-pyflasher-v3.0 / Ps4Exploit-455-By-Draqen-v1.3 for esp8266EX.bin (4.0 MB) / Draqen-Esp8266-405.bin (4.0 MB) / Draqen-Esp8266.bin (4.0 MB) / Draqen-Esp8266-405.bin (4.0 MB) / ESP8266_Simple_455.bin (4.0 MB) / ESP8266_Simple_405.bin (4.0 MB) / Draqen-Esp8266-405.bin (4.0 MB) / Draqen-Esp8266.bin (4.0 MB)
Download: ESP8266XploitHost_fixed2.zip (14.2 MB) / c0d3m4st4_ESP8266XploitHost_nodemcu_1.0b4.zip (967 KB) / c0d3m4st4_ESP8266XploitHost_v1_final.zip (865 KB) / c0d3m4st4_ESP8266XploitHost_v2.0b.zip (1.7 MB) / c0d3m4st4_ESP8266XploitHost_v2.0b2.zip (1.7 MB) /
c0d3m4st4_ESP8266XploitHost_v2.1.zip (1.9 MB)
Finally, from UrbanAnonymous comes a guide on ESP8266 MAC OSX Installation and Flashing for PS4, to quote:
So I am at my core a Windows PC person, but recently I have forced myself to only use a mac to become more familiar with OSX. I am constantly running into situations where I have to figure out how to make things work that only have explanations for windows installs, this is one of them. So for all the time I spent getting the 8266 to connect to my mac and actually complete the process I figured I would compress what I have learned into a tutorial.
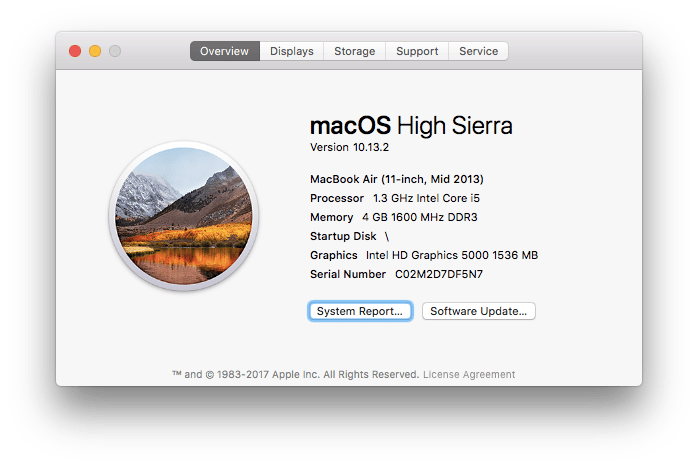
Before I start I want to point out that I am running OSX HIGH SIERRA. The drivers for the ESP8266 may differ depending on what version of OSX u are running and the specific ESP8266 chip you have. You can look on the back of the printed circuit and most will tell you what drivers are needed.
INSTALLING THE ESP8266 ON OSX
FILES TO INSTALL:
So now that you have all the files your gonna need your going to want to install the driver for the esp8266 by selecting and unzipping the driver file u previously downloaded. Once unzipped select the .pkg file and install the drivers. after you are done restart your mac. You should now be able to go to your system information and see the esp8266 under the usb tab. If you are not familiar with how to do this you'll need to go to the apple symbol in the top left corner and select about this mac. It should look something like this.
Then select system report. Once you are in the system report, select the USB tab on the left side of the screen.
You should see something similar to this if the driver installation was successful.
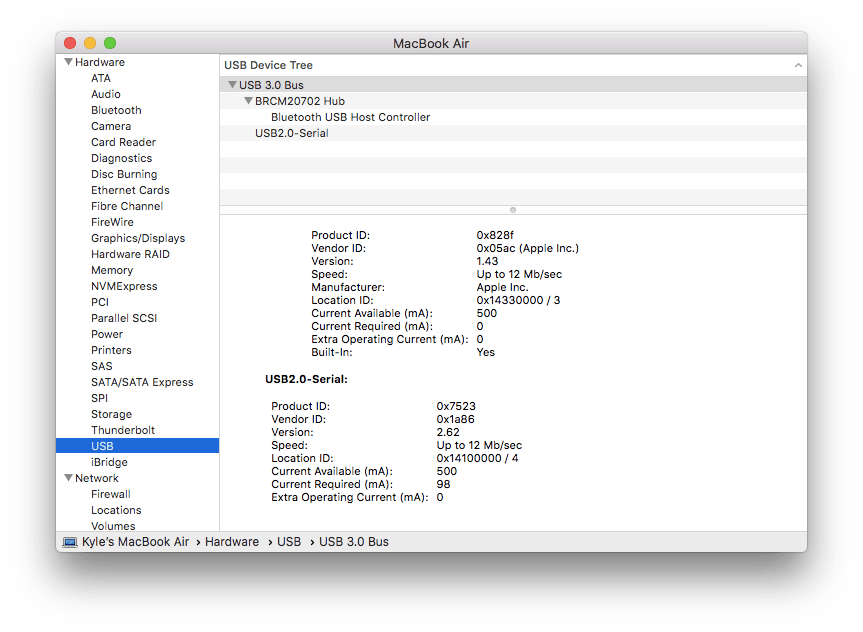
There should be a USB 2.0 device. If you do not see this you can try and find the correct driver for your OSX version or you can comment on this post and ill try my best to help you troubleshoot the issue.
Now you are ready to flash the esp8266 using the NodeMCU-PyFlasher program you previously downloaded. So go ahead and open up the program.
FLASHING PROCEDURE
At this point you should have NodeMCU-PyFlasher open, the rest of this process is pretty simple. your going to want to unzip the firmware file u downloaded (either c0d3m4st4 or RetroGamer74) so that you can load the .BIN file into the flashing software.
We now want to plug the ESP8266 into the PS4 and turn on the system.
PS4 CONFIGURATION
NETWORK CONFIGURATION FOR C0D3M4ST4'S .BIN
Download: PS4Exploit.zip / GIT / ESPS4ExploitServer fork by 5u770n
To quote from the README.md: ESPS4ExploitServer
This is a project for ESP8266 Arduino boards. It has been tested on a (cloned?) Wemos D1 board with 4MByte flash. It uses SPIFFS to load files from the flash chip but can easily be ported to use an SD addon board.
Setting up the board:
- Install the Arduino IDE if you don't already have it
- Start the Arduino IDE Install the ESP8266 library
- Install the ESP8266 Filesystem Uploader - http://www.instructables.com/id/Using-ESP8266-SPIFFS/
- Restart the Arduino IDE Plug in the board and install the drivers for it
- Under Tools: Select the board that is appropriate
- Select the COM port the board is attached to (can be found in the Device Manager in Windows)
- Select the Flash Size - The code is pretty small so you can use the option that has the most memory saved for SPIFFS Ex: 4M (1M/3M SPIFFS)
- Load the .ino from the downloaded directory
- In the /data directory place the payloads that Unplug the board and hold down the Flash button while you plug it back in
- Under Tools, select ESP8266 Sketch Data Uploader
- If there is an error in transferring then unplug the board and hold the Flash button while plugging it back in again
- If there is an error in creating the SPIFFS then you have files adding up to too much memory for what your board so remove some
- Unplug the board and plug it back in Under Sketch, select Upload
Usage:
It defaults to creating an access point 'ps4exploit' with password 'hackmyps4'. Set your PS4 gateway and DNS to 10.13.37.1 when the board is in AP mode. To change the configuration open a web browser to http://10.13.37.1/settings.
Note that it is an unsecured webpage so the password for a wifi network that is entered in will be saved in plain text, but will only be accessible to those that can log onto the network already. In station mode, the IP for the board will attempt to use the default static IP containing '235'. Ex: 192.168.1.1 with subnet mask 255.255.255.0 will try the static IP of 192.168.1.235
Settings:
Selection of wifi mode - AP/Station AP - Network name, password Station - Available networks, password, static IP Payload - Selection of available payloads loaded in flash
Operation:
It creates a web server and fake DNS server that resolves everything back to itself. It defaults back to sending the index.html on any request that doesn't match a file loaded into flash. SPIFFS doesn't allow for directories so the names of the different exploit pages and scripts (and references in their htmls) had to be renamed. Keep this in mind when adding new exploit pages.
If other payload exploit pages are released you must add some code to set JS_MAX to the number of .js files loaded by the page to trigger the automatic payload setting. After the IDC or Specter exploit pages are loaded through a web browser (or user manual on PS4), the payload transfer will automatically start after a 1s wait. If it fails with a not enough memory error then it is best to restart the PS4 because it typically causes a soft-lock on the XMB after repeated attempts.
Failsafes (useful for when you can't reprogram the board): Programmatically - If the board can connect to a wifi station then it will revert back to AP mode If the static IP you select conflicts with the network you connect to then the network will assign one Physically - Bridging D6 to GND while plugging the board into a power source will force it to load up the default AP settings so you can change the network settings (http://10.13.37.1/settings)
Known bugs: The LED doesn't turn on steady after files are transferred (I think the problem is somewhere in the ESP8266 library) Sometimes after a failed payload transfer the board will be stuck in a loop and need to be reset if you can't connect.
Download: ESP8266 ESP32 HTTP OTA server / GIT
Download: Ps4Exploit-455-By-Draqen-v1.2 for esp8266EX.bin (4.0 MB) / nodemcu-pyflasher-v3.0 / Ps4Exploit-455-By-Draqen-v1.3 for esp8266EX.bin (4.0 MB) / Draqen-Esp8266-405.bin (4.0 MB) / Draqen-Esp8266.bin (4.0 MB) / Draqen-Esp8266-405.bin (4.0 MB) / ESP8266_Simple_455.bin (4.0 MB) / ESP8266_Simple_405.bin (4.0 MB) / Draqen-Esp8266-405.bin (4.0 MB) / Draqen-Esp8266.bin (4.0 MB)
Download: ESP8266XploitHost_fixed2.zip (14.2 MB) / c0d3m4st4_ESP8266XploitHost_nodemcu_1.0b4.zip (967 KB) / c0d3m4st4_ESP8266XploitHost_v1_final.zip (865 KB) / c0d3m4st4_ESP8266XploitHost_v2.0b.zip (1.7 MB) / c0d3m4st4_ESP8266XploitHost_v2.0b2.zip (1.7 MB) /
c0d3m4st4_ESP8266XploitHost_v2.1.zip (1.9 MB)
Finally, from UrbanAnonymous comes a guide on ESP8266 MAC OSX Installation and Flashing for PS4, to quote:
So I am at my core a Windows PC person, but recently I have forced myself to only use a mac to become more familiar with OSX. I am constantly running into situations where I have to figure out how to make things work that only have explanations for windows installs, this is one of them. So for all the time I spent getting the 8266 to connect to my mac and actually complete the process I figured I would compress what I have learned into a tutorial.
Before I start I want to point out that I am running OSX HIGH SIERRA. The drivers for the ESP8266 may differ depending on what version of OSX u are running and the specific ESP8266 chip you have. You can look on the back of the printed circuit and most will tell you what drivers are needed.
INSTALLING THE ESP8266 ON OSX
FILES TO INSTALL:
- DRIVERS FOR THE ESP8266 - 210x USB to UART driver (I needed this one) OR CH341SER ESP8266 DRIVERS (Alternative)
- ESP8266 Xploit Host package by c0d3m4st4 (I used this one) OR ESP8266 Xploit Host package by RetroGamer74
So now that you have all the files your gonna need your going to want to install the driver for the esp8266 by selecting and unzipping the driver file u previously downloaded. Once unzipped select the .pkg file and install the drivers. after you are done restart your mac. You should now be able to go to your system information and see the esp8266 under the usb tab. If you are not familiar with how to do this you'll need to go to the apple symbol in the top left corner and select about this mac. It should look something like this.
Then select system report. Once you are in the system report, select the USB tab on the left side of the screen.
You should see something similar to this if the driver installation was successful.
There should be a USB 2.0 device. If you do not see this you can try and find the correct driver for your OSX version or you can comment on this post and ill try my best to help you troubleshoot the issue.
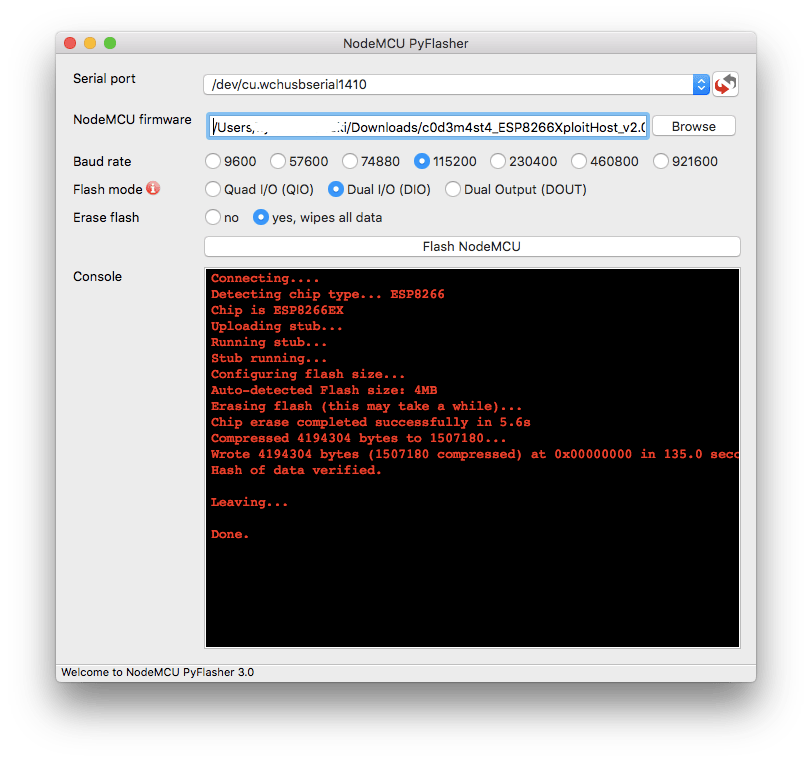
Now you are ready to flash the esp8266 using the NodeMCU-PyFlasher program you previously downloaded. So go ahead and open up the program.
FLASHING PROCEDURE
At this point you should have NodeMCU-PyFlasher open, the rest of this process is pretty simple. your going to want to unzip the firmware file u downloaded (either c0d3m4st4 or RetroGamer74) so that you can load the .BIN file into the flashing software.
- Select the ESP8266 from the drop down menu labeled serial port. My ESP8266 was listed as /dev/cu.wchusbserial1410 (yours may be different).
- For NodeMCU Firmware Select the bin file u recently unzipped. i used c0d3m4st4 which is what you will see in the screenshot below.
- For the Baud rate setting i used the default which is 115200. Alternatively you con look on the back of the printed circuit (on most versions) for the recommended rate.
- Flash mode should be set to Dual I/O (DIO).
- For the erase flash option select "yes, wipes all data".
- Now your going to want to click Flash NodeMCU.
We now want to plug the ESP8266 into the PS4 and turn on the system.
PS4 CONFIGURATION
NETWORK CONFIGURATION FOR C0D3M4ST4'S .BIN
- Go to Settings > Network > Set up internet connection > Use WIFI.
- Select easy then wait for available networks to load.
- once networks are loaded choose “ESP8266XploitHost”
- Use Password “ps4xploit” (without the quotes).
- Test connection, and you are done.
- After that, open the user guide to access the exploit. You can also use it from the PS4 web browser. Just type 13.37.13.37 in the address bar.
- Go to Settings > Network > Set up internet connection > Use WIFI.
- Select custom then wait for available networks to load.
- Once loaded choose "PS4_WIFI"
- Leave all the setting as the default except primary and secondary DNS.
- Set the primary DNS to 10.10.10.1 and do the same for the secondary.
- Test connection and you are done. After that, open the user guide to access the exploit.
- Draqen-Esp8266-fw505-v1.28.bin (4.0 MB) / Archive

