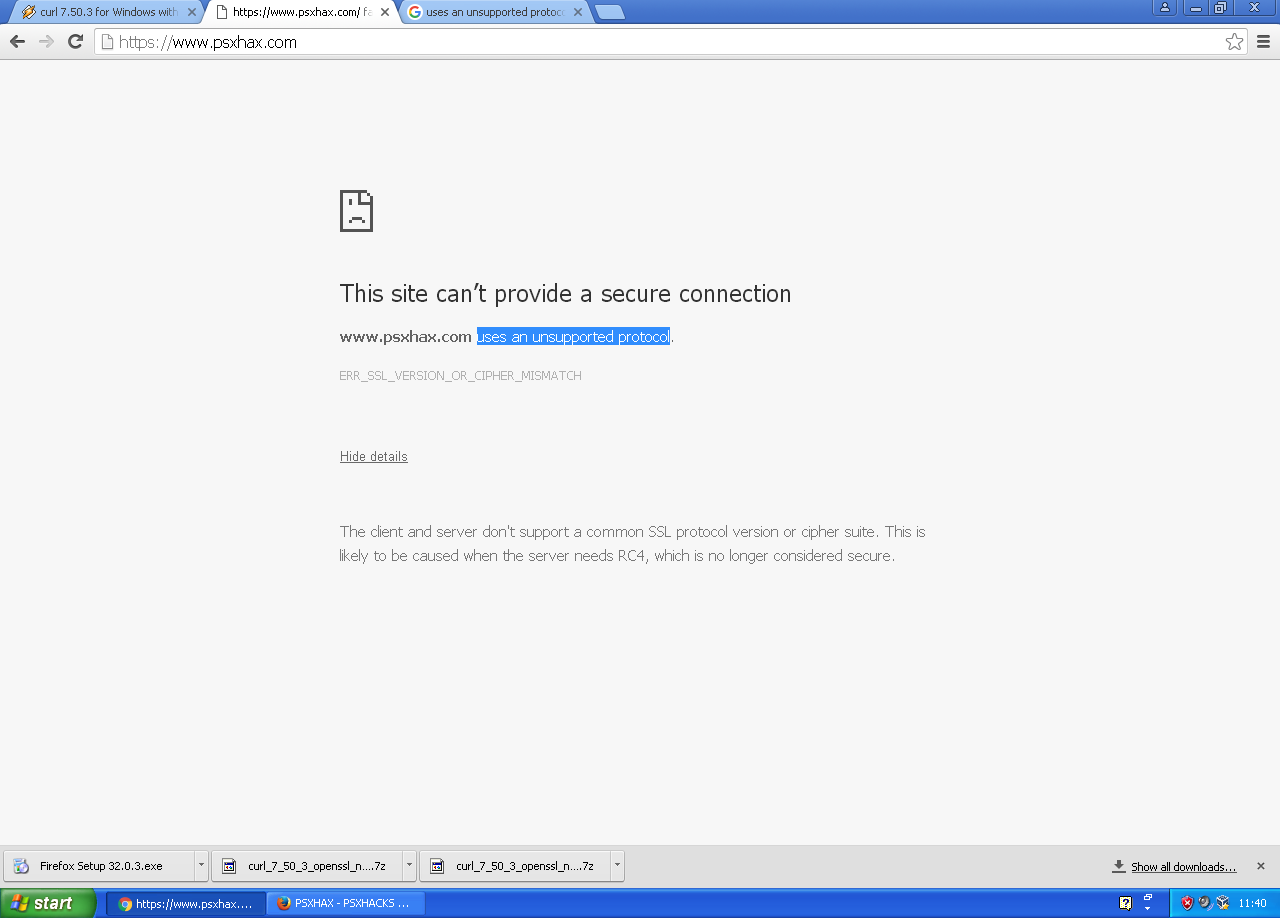
Following the addition of SSL to PSXHAX and some HTTPS assistance a couple of users (including @abzii) were having trouble accessing certain HTTPS sites on Windows XP and XP PRO SP3, and from the title you know that one of these sites was PSXHAX.COM.
I have found a fix for people below who are using certain OS's.
Fix Below
!_____________!
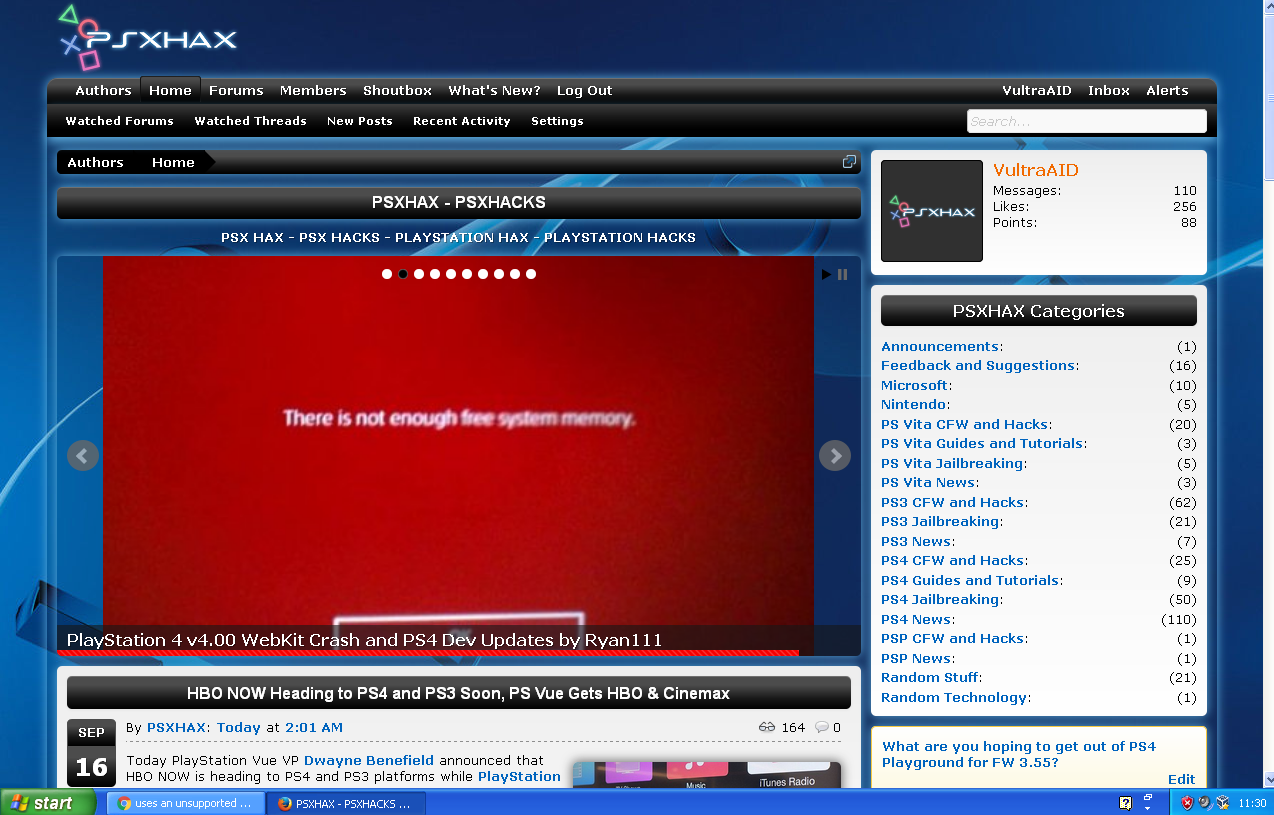
Image: PSXHAX Working on Windows XP Pro SP3 With Firefox
Requirements:
| Windows XP PRO SP3 |
| Firefox 32.0.3 |
| Installing Latest Update For Windows XP |
______________________________________
I was not able to find any real solution other than using downgraded FireForx version 32.0.3. So I would have to continue using FireFox v.32.0.3 whenever I hit that ERR_SSL_VERSION_OR_CIPHER_MISMATCH error in Chrome. Version 33 and 34 may also work - it looks like the latest version of FireFox that still works with SSLv3 would be 34. However, I am using 32.0.3.
Here is the link to install English Win32 version of FireFox v.32.0.3 from Mozilla official FTP site:
Firefox Setup 32.0.3.exe -- 24-Sep-2014 05:21 -- 34Mb
You would need to disable autoupdates so it does not catch that SSLv3 paranoia again:
Menu btn > Options icon > "Update" tab > "Never check for updates"
I was "lucky" that I disabled Firefox updates some time ago and ended up with Firefox version 32 which is not afraid of POODLE and it will be kept that way (i.e. without upgrades), so I have some way to read those poor socially excluded websites with SSL 3.0 next time Chrome shows me
Security Notes

I have found a fix for people below who are using certain OS's.
Fix Below
!_____________!
Image: PSXHAX Working on Windows XP Pro SP3 With Firefox
Requirements:
| Windows XP PRO SP3 |
| Firefox 32.0.3 |
| Installing Latest Update For Windows XP |
______________________________________
I was not able to find any real solution other than using downgraded FireForx version 32.0.3. So I would have to continue using FireFox v.32.0.3 whenever I hit that ERR_SSL_VERSION_OR_CIPHER_MISMATCH error in Chrome. Version 33 and 34 may also work - it looks like the latest version of FireFox that still works with SSLv3 would be 34. However, I am using 32.0.3.
Here is the link to install English Win32 version of FireFox v.32.0.3 from Mozilla official FTP site:
Firefox Setup 32.0.3.exe -- 24-Sep-2014 05:21 -- 34Mb
You would need to disable autoupdates so it does not catch that SSLv3 paranoia again:
Menu btn > Options icon > "Update" tab > "Never check for updates"
I was "lucky" that I disabled Firefox updates some time ago and ended up with Firefox version 32 which is not afraid of POODLE and it will be kept that way (i.e. without upgrades), so I have some way to read those poor socially excluded websites with SSL 3.0 next time Chrome shows me
Security Notes
- If this is your laptop and you often browse from public WiFi, try not to use that FireFox while on a public WiFi, or someone evil may steal your https cookies (below)
- If you do not trust your Internet Provider, delete all existing FireFox cookies and do not ever use that FireFox to login into any sensitive websites, or your evil Internet Provider may steal your https cookies (below).
- The HTTPS site I wanted to connect to only supports old version of TLS called SSL 3.0 or SSLv3
- That version 3.0 of SSL is proven to be insecure, because of the newly discovered POODLE vulnerability (here is much better description of POODLE) which can only be exploited if you ever visit unsecured WiFi with malicious owner who would then trick you to visit his malicious website with certain Javascript (or inject malicious Javascript into non-protected HTTP response from a regular website you are visiting there).
- That malicious Javascript that would need to submit to about 8,000 web requests from your browser to some good site that they know you use, and then, if everything works perfect, they may get to conclude the value of your 32-byte cookie. They would need around 256 requests on average to decrypt one byte. Multiply that with the number of bytes in the cookie, and most often, this attack can be done in seconds or minutes. As far as I understand, even then they would not be able to actually intercept your HTTPS communication. Well, stealing your cookie is bad, don't get me wrong.
- Because I visit WiFi hotspots full of POODLE hackers with my desktop computer in a bag every other day, Google has rightfully decided to protect me from reading those old sites that cannot be reconfigured for using more recent version of SSL, without giving me any option to decide on it. Why is that important? Because for example people run certain hardware that is being administered through HTTPS SSLv3 interface and upgrades are not always possible, for example Tomato and DD-WRT routers - dd-wrt 25408, Asus RT-N66U, Linksys e4200, etc. To see what kind of hoops people have to jump through with Wireshark and lower lever SSL debugging to make their routers back accessible, click here.
- Firefox has followed the suit and disabled the SSLv3 since version 34.
- Copy this to your address bar in chrome: chrome://flags
- Find a setting named "Minimum SSL/TLS version supported."
- Choose SSLv3
- Click on "Relaunch now" button
- Go back to the HTTPS page that was giving you ERR_SSL_VERSION_OR_CIPHER_MISMATCH error
- You will be redirected to a "Your connection is not private" page. If you do not worry about this security issue click on the "Advanced" link.
- Click on "Proceed to <your https page> (unsafe)".

