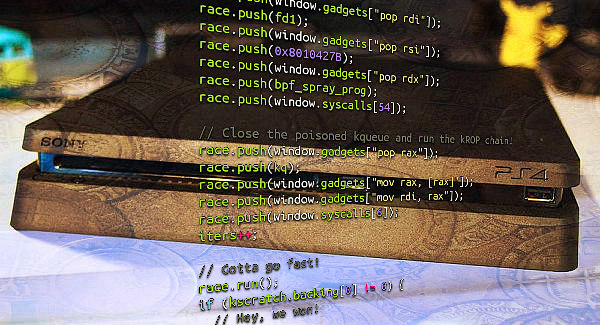
As he did with the 4.05 Kernel Exploit and 4.55 WebKit Exploit, following the initial announcement and 5.05 Kernel Exploit release PlayStation 4 developer @SpecterDev has now made available via Twitter a writeup documenting his PS4 5.05 Kernel Exploit for others to examine and learn from. 
To quote from the PS4 5.05 BPF Double Free Kernel Exploit Writeup.md on Github, in part: Conclusion
Another cool bug to exploit. It should have been a trivial exploit, however Sony's new mitigation that prevents exploit devs from pivoting RSP into userland memory while in kernel context is quite effective, and some tricks had to be used to get the chain into kernel memory - but as demonstrated, it is beatable.
This exploit is also a good example of how double free()'s can be exploited fairly easily on FreeBSD if they're on an object of decent size.
Credits
Additional Thanks
To quote from the PS4 5.05 BPF Double Free Kernel Exploit Writeup.md on Github, in part: Conclusion
Another cool bug to exploit. It should have been a trivial exploit, however Sony's new mitigation that prevents exploit devs from pivoting RSP into userland memory while in kernel context is quite effective, and some tricks had to be used to get the chain into kernel memory - but as demonstrated, it is beatable.
This exploit is also a good example of how double free()'s can be exploited fairly easily on FreeBSD if they're on an object of decent size.
Credits
Additional Thanks
- TheFloW - Suggestions and Feedback
- qwertyoruiopz : Detailed Annotation
- qwertyoruiopz : Zero2Ring0 Slides
- Watson FreeBSD Kernel Cross Reference
- Marco Ramilli : From ROP to JOP
- Wikipedia : Control register (cr0)
- Wikipedia : Critical section

