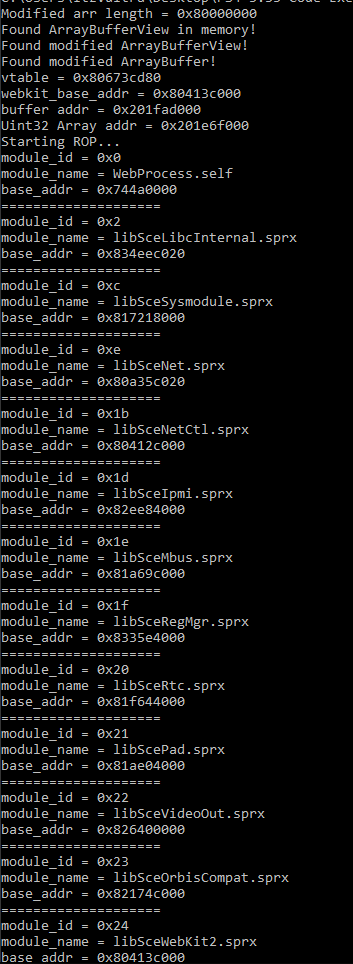
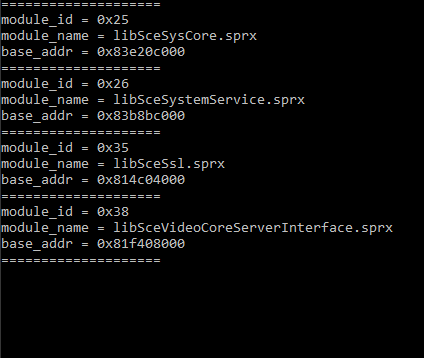
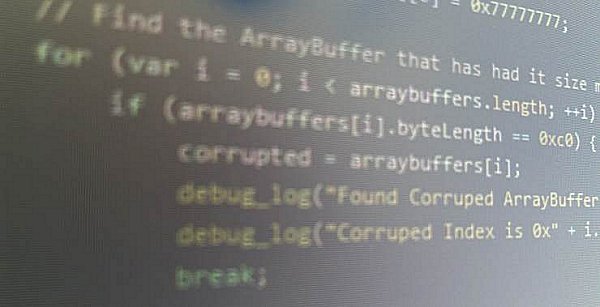
Following the initial release, decryption tutorials and reverse-engineering, PlayStation 4 developer Fire30 (who did the PS4 Webkit Exploit 2.XX PoC) has ported the PlayStation 4 HENkaku exploit allowing PS4 3.55 code execution! 
Download: PS4-3.55-Code-Execution-PoC-master.zip / GIT
Spoiler: Related Tweets
From atreyu187 come some additional details on this HENkaku PS4 port as follows:
"This is only a userland code execution. This is nothing like dlclose or BADIret. We still need an exploit to reach 1.76 level of hacks. Both just mentioned have been patched out of FreeBSD and CTurt has been working with FreeBSD devs to fix the OS making it that much harder. We have had this access opened up in 3.50 already that the WebKit has lead nowhere."
Thanks to @B7U3 C50SS and @Plankton in the Shoutbox and @mcmrc1 in the Forums for sharing the news!
Download: PS4-3.55-Code-Execution-PoC-master.zip / GIT
Spoiler: Related Tweets
From atreyu187 come some additional details on this HENkaku PS4 port as follows:
"This is only a userland code execution. This is nothing like dlclose or BADIret. We still need an exploit to reach 1.76 level of hacks. Both just mentioned have been patched out of FreeBSD and CTurt has been working with FreeBSD devs to fix the OS making it that much harder. We have had this access opened up in 3.50 already that the WebKit has lead nowhere."
Thanks to @B7U3 C50SS and @Plankton in the Shoutbox and @mcmrc1 in the Forums for sharing the news!