Since the initial 1.76 PS4 Playground and 3.55 PS4 Playground for Firmware (WIP) PlayStation 4 developer zecoxao has been working with the help of bigboss, wildcard and droogie on porting the Dlclose Exploit to PS4 Firmware 1.01 in hopes of finding undiscovered bugs and vulnerabilities that may be exploitable! 
Download: PS4 Playground 1.01 (GIT) / SceShellCore.elf (8.97 MB)
According to @zecoxao, to quote: "Most offsets SHOULD be fine and most stuff is working BUT we do NOT have code exec working yet. if anyone knows why, please contact us "
"
From the README.md file: PS4-playground
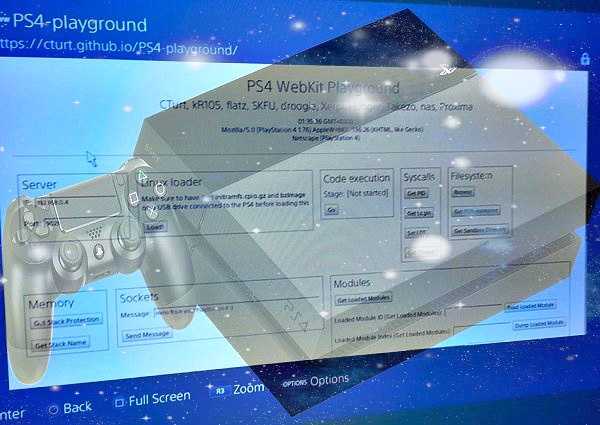
A collection of PS4 tools and experiments using the WebKit exploit. This is for firmware 1.76/1.01 only at the moment.
Although initially just a framework to help write and execute ROP chains, the playground now allows for running unsigned binaries compiled, and booting Linux from USB.
Setup
A live demo can be tried here.
You should clone the repo and upload it your own server if you wish to make changes:
You can also download a zip of the latest source here.
Usage
After executing a test, you should either refresh the page, or close and reopen the browser entirely; running multiple experiments sequentially is not reliable. If you are using a web browser view in an app which isn't the Internet Browser, you can use the Refresh button under Misc to refresh the page.
Code Execution
Click "Go", and wait for the text "Stage: Waiting for payload..." to appear.
Send the desired binary over TCP to your PS4 on port 9023; you can use any standard networking tool to do this, or my custom Windows tool, WiFi-Loader
If you're on Linux, the easiest way is probably to use netcat:
After you have sent the binary, it will be executed automatically.
Linux loader
You need a FAT32 formatted USB drive plugged in on any PS4's USB port with the following files on the root directory:
Syscalls
Patches for decrypt_pup_header (1.76):
Thanks to @ArthurBishop and @Bultra for the heads-up before the weekend in the PSXHAX Shoutbox! 
Download: PS4 Playground 1.01 (GIT) / SceShellCore.elf (8.97 MB)
According to @zecoxao, to quote: "Most offsets SHOULD be fine and most stuff is working BUT we do NOT have code exec working yet. if anyone knows why, please contact us
From the README.md file: PS4-playground
A collection of PS4 tools and experiments using the WebKit exploit. This is for firmware 1.76/1.01 only at the moment.
Although initially just a framework to help write and execute ROP chains, the playground now allows for running unsigned binaries compiled, and booting Linux from USB.
Setup
A live demo can be tried here.
You should clone the repo and upload it your own server if you wish to make changes:
Code:
git clone git://github.com/CTurt/PS4-playground.gitUsage
After executing a test, you should either refresh the page, or close and reopen the browser entirely; running multiple experiments sequentially is not reliable. If you are using a web browser view in an app which isn't the Internet Browser, you can use the Refresh button under Misc to refresh the page.
Code Execution
Click "Go", and wait for the text "Stage: Waiting for payload..." to appear.
Send the desired binary over TCP to your PS4 on port 9023; you can use any standard networking tool to do this, or my custom Windows tool, WiFi-Loader
If you're on Linux, the easiest way is probably to use netcat:
Code:
nc -w 3 192.168.0.7 9023 < *.binLinux loader
You need a FAT32 formatted USB drive plugged in on any PS4's USB port with the following files on the root directory:
- bzImage : Kernel image that will be loaded. Recommended to use this sources to compile it.
- initramfs.cpio.gz : The initial file system that gets loaded into memory during the Linux startup process. This one is recommended.
Syscalls
- Get PID - Get process ID
- Get Login - Get login name and leak a kernel pointer
- Get Loaded Modules - Get a list of currently loaded modules, index and ID
- Dump Loaded Module - Dump a currently loaded module (use Get Loaded Modules to see all available)
- Load Module - Load an additional module from this list
- Once you have loaded a module, refresh the page, and you will be able to dump it.
- Browse - File Browser
- Get PSN username - Read your PSN username from account.dat
- Get Sandbox Directory - Get the name of the current sandbox directory (10 random characters which change each reboot)
- Get Stack Protection - Get stack base, size, and protection
- Get Stack Name - Get stack base, size, and name
- Send Message - Send a TCP message to the specified IP and port
- File and memory dumps will be sent over TCP to the IP and port you specified.
- You can use a simple tool like TCP-Dump to write the data to a file.
Code:
*(uint16_t *)0xFFFFFFFF827E31EE = 0x9090;
*(uint16_t *)0xFFFFFFFF827E31FD = 0x9090;
*(uint16_t *)0xFFFFFFFF827E3202 = 0x9090;
Code:
*(uint16_t *) 0xFFFFFFFF827C445C = 0x9090;
*(uint16_t *) 0xFFFFFFFF827C446B = 0x9090;
*(uint16_t *) 0xFFFFFFFF827C4470 = 0x9090;
