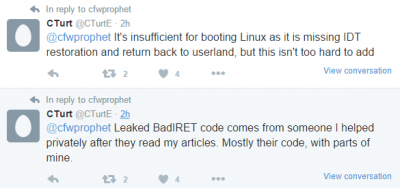
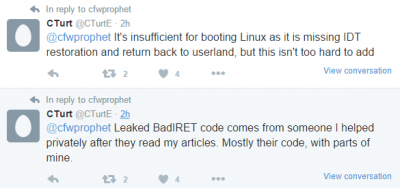
Today 'anonymous' hacker AK471337 has leaked the PS4 BadIRET Kernel Exploit source code according to PlayStation 4 developer CTurt, with details below from my post on PS4 News and the related Tweets below!
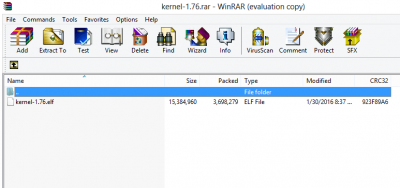
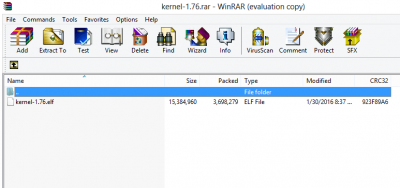
Download: PS4-Bad-IRET-master.zip / PS4-Bad-IRET-master.zip (Mirror) / PS4 Dongle.txt via choppa / kernel-1.76.rar via DotExE01 / badiret.bin (Compiled) by KUNITOKI via 2424marco / PS4-Bad-IRET-master-2.bin (Updated Mirror) / PS4-Bad-IRET-5fs.bin (Updated Mirror #2)
From Wololo comes some additional details as follows, to quote:
PS4 Kernel exploit – is it good news for you?
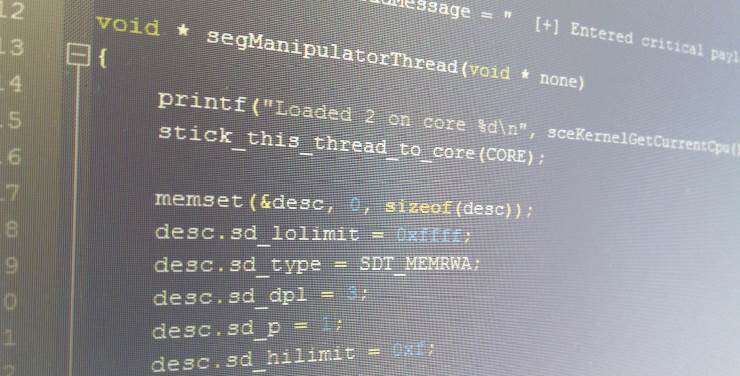
If you’re an en user with no programming skills, this exploit won’t be useful for you. You’d have to compile it and run it on a PS4 on firmware 1.76, through the 1.76 webkit userland exploit. (The Kernel exploit might work up to firmwares 2.xx, but then you’d need to find an unpatched userland exploit in order to run it)
 If you have some programming skills and happen to own a PS4 1.76 however, this could be a nice entry point for you to understand how these things are done. If you get to display the debug message from the kernel exploit (Entered Critical Payload), you’re pretty much ahead of 99.99% of the PS4 homebrew community today.
If you have some programming skills and happen to own a PS4 1.76 however, this could be a nice entry point for you to understand how these things are done. If you get to display the debug message from the kernel exploit (Entered Critical Payload), you’re pretty much ahead of 99.99% of the PS4 homebrew community today.
But if you’re an “end user” and can get a 1.76 PS4, this could mean someone might be able to release PS4 Linux for you sooner than later.
More generally however, as I’ve stated before, people with the right set of skills could probably have figured out the exploit thanks to CTurt's detailed explanation. This release probably doesn’t change much who’s going to work on exploiting the PSP in the foreseeable future.
How the leak happened
Rumors say someone was able to grab passwords from several well known hackers of the PS4 scene, and managed to work his way into a private github where the files were stored. There is a strong reminder here for all of us that you should have different passwords on all the sites you visit, to avoid becoming the weakest link in such a situation.
 There’s a group of people who believe leaking such information is a good thing for the scene as it spreads the information. In my opinion, hackers often have very good reasons to not share their hacks, often because they are not ready for public consumption, and as such are useless to the vast majority of users. A hack that leaks at the wrong time could typically be patched by the manufacturer before it is even made usable for the scene.
There’s a group of people who believe leaking such information is a good thing for the scene as it spreads the information. In my opinion, hackers often have very good reasons to not share their hacks, often because they are not ready for public consumption, and as such are useless to the vast majority of users. A hack that leaks at the wrong time could typically be patched by the manufacturer before it is even made usable for the scene.
The BadIRET exploit however has already been patched by Sony a long time ago, so it leaking is probably not a massive problem for the scene... What do you think? This is exciting news, but also a bit sad given the circumstances of the release.
From choppa: I found this ?
From CTurt: 9/11 Leak was an inside job.
While this may indeed be a legitimate leak, it could also be a planned insider leak with rumors of an upcoming PS4 Cobra USB Game Emulator DRM Device... time will tell for sure.
Download: PS4-Bad-IRET-master.zip / PS4-Bad-IRET-master.zip (Mirror) / PS4 Dongle.txt via choppa / kernel-1.76.rar via DotExE01 / badiret.bin (Compiled) by KUNITOKI via 2424marco / PS4-Bad-IRET-master-2.bin (Updated Mirror) / PS4-Bad-IRET-5fs.bin (Updated Mirror #2)
From Wololo comes some additional details as follows, to quote:
PS4 Kernel exploit – is it good news for you?
If you’re an en user with no programming skills, this exploit won’t be useful for you. You’d have to compile it and run it on a PS4 on firmware 1.76, through the 1.76 webkit userland exploit. (The Kernel exploit might work up to firmwares 2.xx, but then you’d need to find an unpatched userland exploit in order to run it)
 If you have some programming skills and happen to own a PS4 1.76 however, this could be a nice entry point for you to understand how these things are done. If you get to display the debug message from the kernel exploit (Entered Critical Payload), you’re pretty much ahead of 99.99% of the PS4 homebrew community today.
If you have some programming skills and happen to own a PS4 1.76 however, this could be a nice entry point for you to understand how these things are done. If you get to display the debug message from the kernel exploit (Entered Critical Payload), you’re pretty much ahead of 99.99% of the PS4 homebrew community today.But if you’re an “end user” and can get a 1.76 PS4, this could mean someone might be able to release PS4 Linux for you sooner than later.
More generally however, as I’ve stated before, people with the right set of skills could probably have figured out the exploit thanks to CTurt's detailed explanation. This release probably doesn’t change much who’s going to work on exploiting the PSP in the foreseeable future.
How the leak happened
Rumors say someone was able to grab passwords from several well known hackers of the PS4 scene, and managed to work his way into a private github where the files were stored. There is a strong reminder here for all of us that you should have different passwords on all the sites you visit, to avoid becoming the weakest link in such a situation.
 There’s a group of people who believe leaking such information is a good thing for the scene as it spreads the information. In my opinion, hackers often have very good reasons to not share their hacks, often because they are not ready for public consumption, and as such are useless to the vast majority of users. A hack that leaks at the wrong time could typically be patched by the manufacturer before it is even made usable for the scene.
There’s a group of people who believe leaking such information is a good thing for the scene as it spreads the information. In my opinion, hackers often have very good reasons to not share their hacks, often because they are not ready for public consumption, and as such are useless to the vast majority of users. A hack that leaks at the wrong time could typically be patched by the manufacturer before it is even made usable for the scene.The BadIRET exploit however has already been patched by Sony a long time ago, so it leaking is probably not a massive problem for the scene... What do you think? This is exciting news, but also a bit sad given the circumstances of the release.
From choppa: I found this ?
Code:
PS4 Dongle
#include
#include
int _netdebug_sock;
#define debug(…)\
do {\
char buffer[512];\
int size = sprintf(buffer, ##__VA_ARGS__);\
sceNetSend(_netdebug_sock, buffer, size, 0);\
} while(0)
/*———————————————————————–*/
/* Program Main */
/*———————————————————————–*/
#define SIZE_OF_BUFFER 512 //64
int _main(void)
{
// Init and resolve libraries
initKernel();
initLibc();
initNetwork();
initUsb();
struct sockaddr_in server;
server.sin_len = sizeof(server);
server.sin_family = AF_INET;
server.sin_addr.s_addr = IP(192, 168, 0, 5);
server.sin_port = sceNetHtons(9023);
memset(server.sin_zero, 0, sizeof(server.sin_zero));
_netdebug_sock = sceNetSocket(“netdebug”, AF_INET, SOCK_STREAM, 0);
sceNetConnect(_netdebug_sock, (struct sockaddr *)&server, sizeof(server));
FATFS fatfs; /* File system object */
FATFS_DIR dir; /* Directory object */
// FILINFO fno; /* File information object */
WORD i;
BYTE buff[SIZE_OF_BUFFER];
FRESULT rc;
FATFS FatFs; /* FatFs work area needed for each volume */
FATFS_FIL Fil; /* File object needed for each open file */
UINT bw, br;
debug(“\nMount a volume.\n”);
rc = f_mount(&fatfs, “”, 0); /* Give a work area to the default drive */
if (rc) debug(“die\n”);
debug(“\nOpen a test file (message.txt).\n”);
// open an existing file with read access
if (f_open(&Fil, “Fuses.txt”, FA_READ | FA_OPEN_EXISTING) == FR_OK) /* Create a file */
{
debug(“\nType the file content.\n”);
for (;;)
{
rc = f_read(&Fil, &buff, SIZE_OF_BUFFER, &br);
if (rc || !br) break; // Error or end of file
for (i = 0; i < br; i++) // Type the data
debug("%c", buff[i]);
}
if (rc) debug("die\n");
f_close(&Fil); /* Close the file */
}
if (rc) debug("die\n");
debug("File Read Complete.\n");
debug("\nTest completed.\n");
disk_deinitialize ();
sceNetSocketClose(_netdebug_sock);
return ;
}
/*———————————————————*/
/* User Provided Timer Function for FatFs module */
/*———————————————————*/
DWORD get_fattime (void)
{
return ((DWORD)(2010 – 1980) << 25) /* Fixed to Jan. 1, 2010 */
| ((DWORD)1 << 21)
| ((DWORD)1 << 16)
| ((DWORD)0 << 11)
| ((DWORD)0 <> 1);While this may indeed be a legitimate leak, it could also be a planned insider leak with rumors of an upcoming PS4 Cobra USB Game Emulator DRM Device... time will tell for sure.

