Since his PS4 Save Mounter Utility release, the PS4 6.20 ROP Execution Method, PS4 Webkit Bad_Hoist Exploit, 7.02 PS4 KEX, PS4 Webkit Exploit 6.72 Port, PS4 6.72 Jailbreak Exploit, Backporting PS4 Instructions, ESP8266 Xploit 6.72 Host and 6.72 PS4 Exploit Menu today ChendoChap shared a PS4 IPv6 UAF 6.70-6.72 Kernel Exploit implementation with patches that may be more stable according to @SpecterDev on Twitter! 
Download: ps4-ipv6-uaf-master.zip / GIT / Test Page / Test 2 / Test 3 via Leeful / PS4 PayLoad Sender.rar (31.9 MB) / Test Page via @RetroGamer74 on Twitter
Other PlayStation 4 Firmware Revisions with Patches Included via fabrebatalla18:
Summary
In this project you will find a full implementation of the "ipv6 uaf" kernel exploit for the PlayStation 4 on 6.70 - 6.72. It will allow you to run arbitrary code as kernel, to allow jailbreaking and kernel-level modifications to the system. will launch the usual payload launcher (on port 9020).
This bug was originally discovered by Fire30, and subsequently found by Andy Nguyen
Patches Included
The following patches are applied to the kernel:
 Some tips...
Some tips...
1) When you navigate to the site, you will get an "There is not enough free system memory." message if it is successful, any other message means restart your PS4.
2) Once you see this message, DON'T press OK! Press the PS button
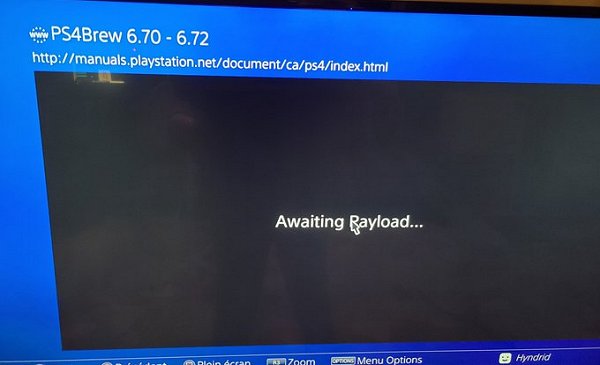
3) Re-open site -> Awaiting Payload
 Also heating things up in the PS4 scene today is a 6.72 WebRTE Payload from @TylerMods of PS4Trainer.com with some additional details in the Tweets below via kiwidoggie for what's to come including PS4 injectable trainers using Mira:
Also heating things up in the PS4 scene today is a 6.72 WebRTE Payload from @TylerMods of PS4Trainer.com with some additional details in the Tweets below via kiwidoggie for what's to come including PS4 injectable trainers using Mira:
Testing new PS4 Kernel Exploit (IPV6 for 7.02) in 5.05 FW
Cheers to @S3phi40T, @SocraticBliss, @SpecterDev and @DEFAULTDNB for the heads up and @hyndrid for the screenshot below on this great progress update!
Download: ps4-ipv6-uaf-master.zip / GIT / Test Page / Test 2 / Test 3 via Leeful / PS4 PayLoad Sender.rar (31.9 MB) / Test Page via @RetroGamer74 on Twitter
Other PlayStation 4 Firmware Revisions with Patches Included via fabrebatalla18:
- PS4 5.05 Kernel Exploit
- PS4 5.50 Kernel Exploit
- PS4 5.53 Kernel Exploit
- PS4 5.55-5.56 Kernel Exploit
- PS4 6.00-6.02 Kernel Exploit
- PS4 6.20 Kernel Exploit
- PS4 6.50-6.51 Kernel Exploit
Summary
In this project you will find a full implementation of the "ipv6 uaf" kernel exploit for the PlayStation 4 on 6.70 - 6.72. It will allow you to run arbitrary code as kernel, to allow jailbreaking and kernel-level modifications to the system. will launch the usual payload launcher (on port 9020).
This bug was originally discovered by Fire30, and subsequently found by Andy Nguyen
Patches Included
The following patches are applied to the kernel:
- Allow RWX (read-write-execute) memory mapping (mmap / mprotect)
- Syscall instruction allowed anywhere
- Dynamic Resolving (sys_dynlib_dlsym) allowed from any process
- Custom system call #11 (kexec()) to execute arbitrary code in kernel mode
- Allow unprivileged users to call setuid(0) successfully. Works as a status check, doubles as a privilege escalation.
- The page will crash on successful kernel exploitation, this is normal
- There are a few races involved with this exploit, losing one of them and attempting the exploit again might not immediately crash the system but stability will take a hit.
- Specter - advice + 5.05 webkit and (6.20) rop execution method
- kiwidog - advice
- Fire30 - bad_hoist
- Andy Nguyen - disclosed exploit code
- SocraticBliss - Shakespeare dev & crash test dummy
1) When you navigate to the site, you will get an "There is not enough free system memory." message if it is successful, any other message means restart your PS4.
2) Once you see this message, DON'T press OK! Press the PS button
3) Re-open site -> Awaiting Payload
Testing new PS4 Kernel Exploit (IPV6 for 7.02) in 5.05 FW
Cheers to @S3phi40T, @SocraticBliss, @SpecterDev and @DEFAULTDNB for the heads up and @hyndrid for the screenshot below on this great progress update!

