Proceeding the Ricochet Anti-Cheat Kernel-Level Driver, PS4_Cheater Homebrew App for 9.00 and MW2 Remastered PS4 Mod Menu Loader for 9.00 today developer Avan06 (aka @avan) released a Beta of his PS4CheaterNeo Application to find PS4 Game Cheat Codes based on PS4Debug and .Net Framework 4.8 for the PlayStation 4 Scene to test out. 
Download: PS4CheaterNeo (Latest Version) (includes PS4CheaterNeo.exe, Be.Windows.Forms.HexBox.dll, GroupGridView.dll and libdebug.dll) / GIT
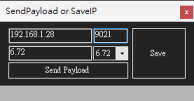
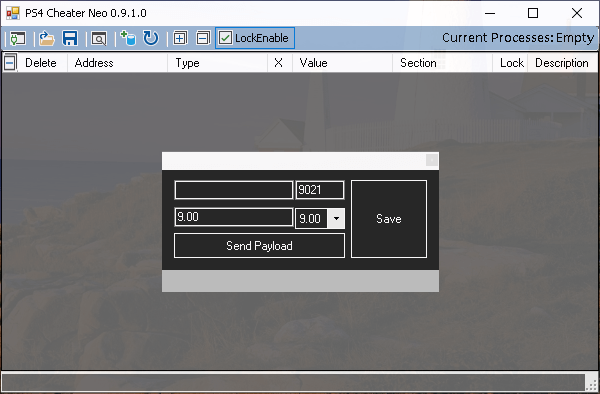
He notes that if you want to execute SendPayload to enable ps4debug, you must manually download ps4debug.bin and place it in the specified directory: the same path as PS4CheaterNeo.exe\payloads\[FW version]\ directory.
Here's more from the README.md: PS4CheaterNeo
Overview
PS4CheaterNeo is a program to find game cheat codes, and it is based on ps4debug and .Net Framework 4.8. Currently in beta:
Table of Contents
TOC generated by markdown-toc
Building
ps4debug
Add Address
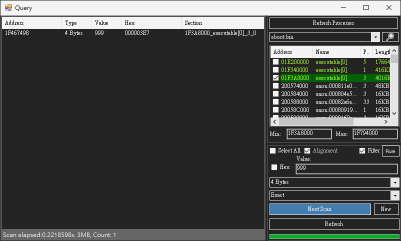
Query window
Section
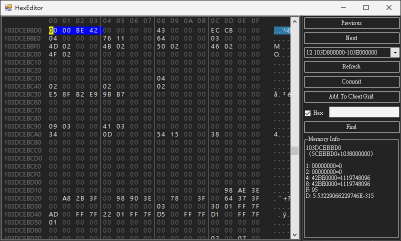
Hex Editor
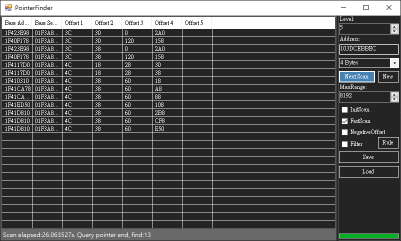
Pointer Finder

Reference
Cheers to MSZ_MGS for the initial heads-up on this project via Twitter!
Download: PS4CheaterNeo (Latest Version) (includes PS4CheaterNeo.exe, Be.Windows.Forms.HexBox.dll, GroupGridView.dll and libdebug.dll) / GIT
He notes that if you want to execute SendPayload to enable ps4debug, you must manually download ps4debug.bin and place it in the specified directory: the same path as PS4CheaterNeo.exe\payloads\[FW version]\ directory.
Here's more from the README.md: PS4CheaterNeo
Overview
PS4CheaterNeo is a program to find game cheat codes, and it is based on ps4debug and .Net Framework 4.8. Currently in beta:
Table of Contents
TOC generated by markdown-toc
Building
- Open PS4CheaterNeo.sln with Visual Studio (Community also available) and built with .Net Framework 4.8.
- User interface re-layout and design to dark mode.
- The cheat window and the query window are separated.
- Hex Editor can be opened from the cheat or query window.
- Pointer finder can be executed from the cheat or query lists.
- Opening the PS4CheaterNeo program will automatically detect whether ps4debug is enabled.
- If not enabled, SendPayload will be executed to enable ps4debug.
- You must specify the ps4 connection IP in SendPayload.
- SendPayload requires the ps4debug.bin file that conforms to the FW version.
- Port is 9090 when using GoldHEN2.0b to Enable BinLoader Server, Other Bin Loader tool port is usually 9021.
ps4debug
- You must manually copy ps4debug.bin to the same path as PS4CheaterNeo.exe\payloads\[FW version]\ directory.
Code:
path\PS4CheaterNeo\bin\Debug\payloads\[FW version]\ps4debug.bin
path\PS4CheaterNeo\bin\Release\payloads\[FW version]\ps4debug.bin- It can be downloaded at the following URL (Only ps4debug 6.72 has been tested).
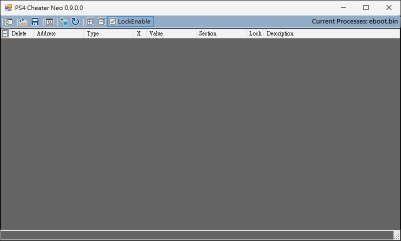
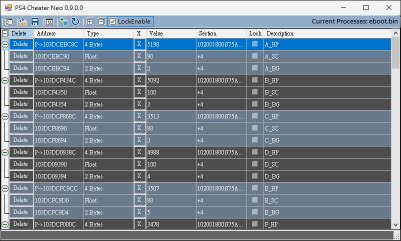
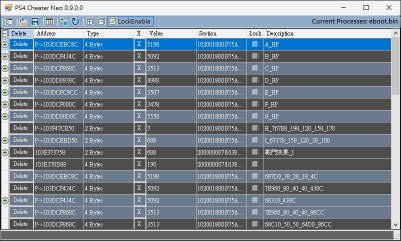
- The cheat list can be loaded with cheats file, and the cheat value can be edited and locked.
- The cheat list has a group expandable/collapsible mechanism, and the cheat description with the same beginning will be set to the same group.
- You can add the address to the Cheat List from the Query window or Hex Editor, and can also be added manually.
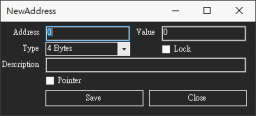
Add Address
- You can manually add addresses to the Cheat List.
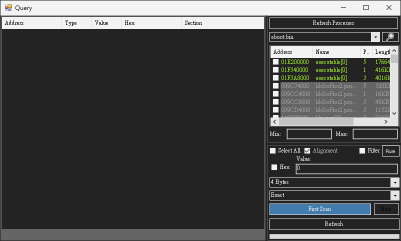
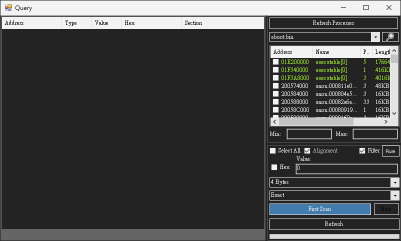
Query window
- Opening the query window will automatically refresh processes list, if eboot.bin already exists it will be selected.
- Support query multiple targets, Multiple query windows can be opened at the same time.
- In addition to query types such as Byte, Float, Double, Hex, etc., it also supports Group types.
- Make the section of the suspected target more obvious.
- The query value will skip the filtered section list when the filter checkbox is clicked.
- The preset section filter rules is libSce, libc.prx, SceShell, SceLib, SceNp, SceVoice, SceFios, libkernel, SceVdec, these rules can also be customized.
Section
- The memory address of the PS4 game is the start position of the specific section plus the relative offset value.
- The start position of sections is dynamic and will change every time you start the game or load the game save or just go through a scene in the game.
- This program will reload the sections when executes the lock or refresh the cheat codes to ensure that it is correct.
- Use group search when you already know the data structure of the query target.
- Input format: [ValueType1:]ValueNumber1 [,] [ValueType2:]ValueNumber2 [,] [ValueType3:]ValueNumber3...
- The ValueType can be 1(Byte), 2(2 Bytes), 4(4 Bytes), 8(8 Bytes), F(Float), D(Double), H(Hex) or not specified.
- The ValueType is preset to 4 bytes when the value type is not specified.
- The ValueNumber can be specified as an asterisk(*) or question mark(?) when the value is unknown.
- The delimiter can be comma(,) or space( ).
Code:
Assuming the target structure is 63 00 E7 03 00 00 AB CD 00 00 00 01
Group scan can be entered as 2:99 999 ? 2:256- Display the detailed information values of the address value of the current cursor position.
- Make address values greater than zero more obvious.
- You can add the address to the Cheat List from the current cursor position.
Pointer Finder
- Make the base address of the pointer be in the executable section when FastScan is clicked.
- If there is no result, you can try to click NegativeOffset.
- The finder will skip the filtered section list when the filter checkbox is clicked.
- The preset section filter rules is libSce, libc.prx, SceShell, SceLib, SceNp, SceVoice, SceFios, libkernel, SceVdec, these rules can also be customized.
Reference
Cheers to MSZ_MGS for the initial heads-up on this project via Twitter!


