Since his previous release and the update, today PlayStation 4 developer @Mistawes made available via Twitter FTPS4 with ELF decrypting and integrated PS4API a.k.a FTPS4API 4.55. 
Download: FTPS4-4.55.zip / FTPS4 (Latest) / GIT / ftps4-jkpatch-payload.bin
Also below are some recent Tweets making their rounds on the Twitter circuit earlier, and from the README.md: FTPS4
FTP server for PS4 with root access, UART, full debug settings - credits: WildCard, Specter, IDC, Shadow, Xerpi.
Finally, from zecoxao comes a brief guide on How to Validate Your ELFs Decrypted Using MMAP Trick
To quote: Special Thanks to Anonymous for helping me with this, and to softstar for providing the ELFs.
You'll need:
Step 2: Grab the encrypted SceShellCore (at /system/vsh/)
Step 3: Use custom DECRYPT command (in filezilla, this can be found in Server->Indicate personalized command...)
Step 4: Grab decrypted SceShellCore (same location but now DECRYPT is toggled ON)
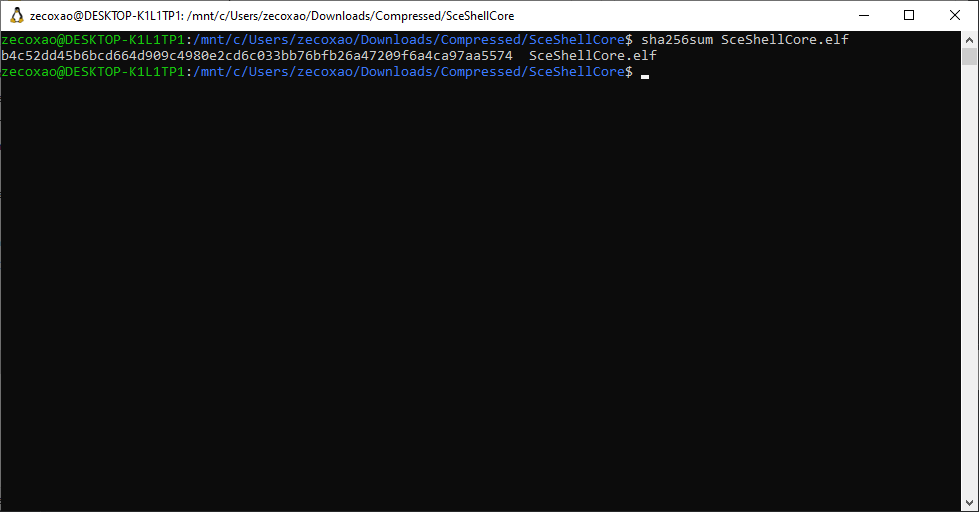
Step 5: Hash the decrypted elf (sha256sum SceShellCore.elf)
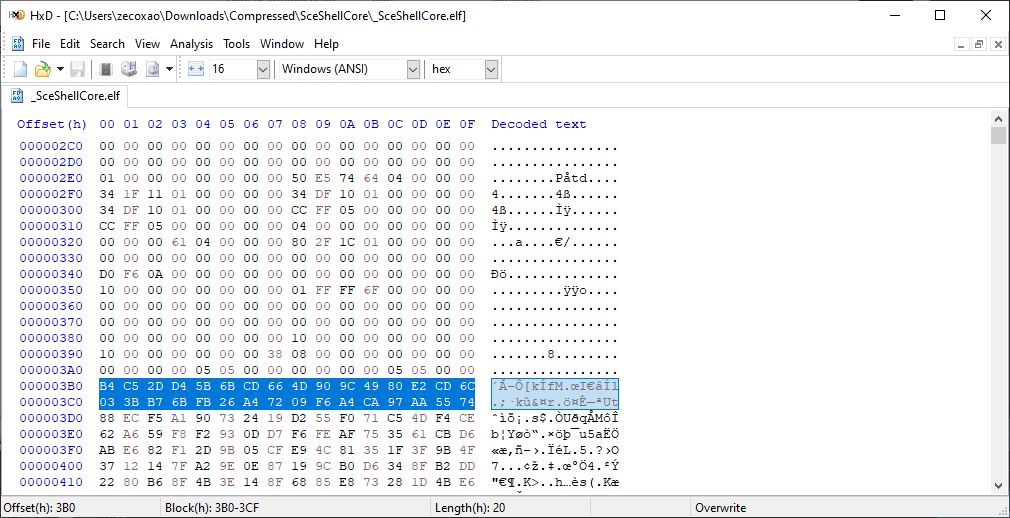
Step 6: Compare it with the FIRST 0x20 bytes that look like random data. If they match, your elf is OK, if they don't match, retry to download the elf with DECRYPT toggled on until it matches.
This concludes the tutorial. Some pics:

Download: FTPS4-4.55.zip / FTPS4 (Latest) / GIT / ftps4-jkpatch-payload.bin
Also below are some recent Tweets making their rounds on the Twitter circuit earlier, and from the README.md: FTPS4
FTP server for PS4 with root access, UART, full debug settings - credits: WildCard, Specter, IDC, Shadow, Xerpi.
Finally, from zecoxao comes a brief guide on How to Validate Your ELFs Decrypted Using MMAP Trick
To quote: Special Thanks to Anonymous for helping me with this, and to softstar for providing the ELFs.
You'll need:
- An FTP Payload with CUSTOM DECRYPT command (you can compile it from scene-collective github repo)
- A target file (I've chosen 5.05's SceShellCore for this) in both encrypted and decrypted state.
- Filezilla
- Hashing tool (I use WSL with sha256sum tool)
Step 2: Grab the encrypted SceShellCore (at /system/vsh/)
Step 3: Use custom DECRYPT command (in filezilla, this can be found in Server->Indicate personalized command...)
Step 4: Grab decrypted SceShellCore (same location but now DECRYPT is toggled ON)
Step 5: Hash the decrypted elf (sha256sum SceShellCore.elf)
Step 6: Compare it with the FIRST 0x20 bytes that look like random data. If they match, your elf is OK, if they don't match, retry to download the elf with DECRYPT toggled on until it matches.
This concludes the tutorial. Some pics:

