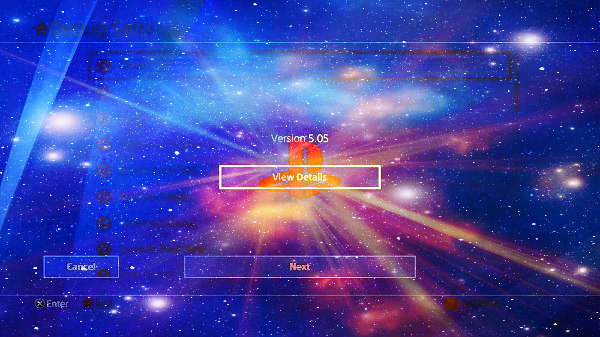
Following his 5.05 PS4 Jailbreak announcement and the release of Project Mira v1.0, PlayStation 4 developer @SpecterDev made available on Twitter a roadmap for the PS4 Homebrew Toolchain alongside a js_shellcode.py Python script to convert payloads to shellcode and of course the 5.05 kernel exploit stack release itself, which as he states "includes the kexploit that autolaunches homebrew patches and Mira. On subsequent page loads it listens for payloads." 
Download: PS4-5.05-Kernel-Exploit-master.zip / GIT / Live Demo / Live Demo (Mirror) / 505-KernelDumper-master.zip / GIT / PS4 Kernel Dumper (AIO) / PS4-Kernel-Dumper.bin / GIT by eversion
PlayStation 4 developer qwertyoruiop also shared a Live Demo (linked above) of the PS4 5.05 kernel exploit BPF setf double free implementation including Mira + XVortexHEN and VVildCard777 made available a PS4 5.05 Kernel Dumper which can also be found linked above.
Several members have reported that the PS4 5.05 Kernel Exploit also works on 5.07 OFW including edrix2004 and MICHY, while @Al Azif added 5.05 support to his v0.4.2 Host and icekuv shared a guide to run the 5.05 kexploit locally with an exploit host file pack from Cyb3rr.
Including some from XVortex and Codsworth for ESP8266 Devices there are already several PS4 5.05 Payload updates with video demos and guides below, and those seeking the PS4 5.05 OFW PUP and Recovery files to Update to a Specific Firmware instead of Sony's latest can find them in several mirrors (such as HERE and HERE) within this thread and also linked HERE in the archive... just remember if you previously used the PS4 Update Blocker to follow iSCORPION's tip to temporarily disable it.
From the README.md: PS4 5.05 Kernel Exploit
Summary
In this project you will find a full implementation of the second "bpf" kernel exploit for the PlayStation 4 on 5.05. It will allow you to run arbitrary code as kernel, to allow jailbreaking and kernel-level modifications to the system. This exploit also contains autolaunching code for Mira and Vortex's HEN payload. Subsequent loads will launch the usual payload launcher.
This bug was discovered by qwertyoruiopz, and can be found hosted on his website here. The GitHub Pages site automatically generated from this repository should also work.
Patches Included
The following patches are made by default in the kernel ROP chain:
Massive credits to the following:
Compile with your PC's IP listening on port 9023
On PC you can do to listen: socat - tcp-listen:9023 > kernelDump.bin
and to send: socat -u FILE:payload.bin TCP:"PS4 IP":9020
you can then trim out the socket prints or you can adapt it with 2 sockets, one for dumping, another for logging.
To compile for 5.05 you need to use an *** with changes for 5.05 support, i have used https://github.com/xvortex/ps4-payload-***
PS4 5.05 Jailbreak by seanp2500
PS4 5.05 Jailbreak Tutorial by MODDED_WARFARE
5.05 Installing Package Files (PS4/PS2 Games & Custom Themes) by MODDED_WARFARE
5.05 Kernel Exploit Full Tutorial by Andrew Marques
PS4 Pr0 5.05 Debug Menu by GrimDoe
PS4 Pr0 5.05 / PS2 (Mortal Kombat - Armageddon) by GrimDoe
How to Jailbreak PS4 5.05 Jailbreak Tutorial
A few notes on the 5.05 exploit:
1) The page will crash after the kernel exploit successfully runs, this is normal
2) First load after successful exploitation will autoload HEN and Mira (can get klog by nc [ps4 ip] 9998
3) Subsequent loads go to the usual payload launcher.
This is for those who don't like reading manuals, or simply can't read.
IP: 13.37.13.37
AP: ESP8266XploitHost
AP Password: ps4xploit (you can change it from the tools menu)
FTP user: ps4xploit
FTP password: ps4xploit (if you change the AP pass, this one will change too,)
Port: 21
PS4 Fan Speed for 5.05 Kernel thanks to TheoryWrong:
Download: kernel-505dev.elf (14.65 MB)
Download: 505_fself.bin (1.32 MB)
Download: PS4-5.05-Kernel-Exploit-master.zip / GIT / Live Demo / Live Demo (Mirror) / 505-KernelDumper-master.zip / GIT / PS4 Kernel Dumper (AIO) / PS4-Kernel-Dumper.bin / GIT by eversion
PlayStation 4 developer qwertyoruiop also shared a Live Demo (linked above) of the PS4 5.05 kernel exploit BPF setf double free implementation including Mira + XVortexHEN and VVildCard777 made available a PS4 5.05 Kernel Dumper which can also be found linked above.
Several members have reported that the PS4 5.05 Kernel Exploit also works on 5.07 OFW including edrix2004 and MICHY, while @Al Azif added 5.05 support to his v0.4.2 Host and icekuv shared a guide to run the 5.05 kexploit locally with an exploit host file pack from Cyb3rr.
Including some from XVortex and Codsworth for ESP8266 Devices there are already several PS4 5.05 Payload updates with video demos and guides below, and those seeking the PS4 5.05 OFW PUP and Recovery files to Update to a Specific Firmware instead of Sony's latest can find them in several mirrors (such as HERE and HERE) within this thread and also linked HERE in the archive... just remember if you previously used the PS4 Update Blocker to follow iSCORPION's tip to temporarily disable it.
From the README.md: PS4 5.05 Kernel Exploit
Summary
In this project you will find a full implementation of the second "bpf" kernel exploit for the PlayStation 4 on 5.05. It will allow you to run arbitrary code as kernel, to allow jailbreaking and kernel-level modifications to the system. This exploit also contains autolaunching code for Mira and Vortex's HEN payload. Subsequent loads will launch the usual payload launcher.
This bug was discovered by qwertyoruiopz, and can be found hosted on his website here. The GitHub Pages site automatically generated from this repository should also work.
Patches Included
The following patches are made by default in the kernel ROP chain:
- Disable kernel write protection
- Allow RWX (read-write-execute) memory mapping
- Syscall instruction allowed anywhere
- Dynamic Resolving (sys_dynlib_dlsym) allowed from any process
- Custom system call #11 (kexec()) to execute arbitrary code in kernel mode
- Allow unprivileged users to call setuid(0) successfully. Works as a status check, doubles as a privilege escalation.
- Vortex's HEN (Homebrew Enabler)
- Mira
- The page will crash on successful kernel exploitation, this is normal
Massive credits to the following:
- qwertyoruiopz
- Flatz
- Vortex
- OpenOrbis Team
- Anonymous
Compile with your PC's IP listening on port 9023
On PC you can do to listen: socat - tcp-listen:9023 > kernelDump.bin
and to send: socat -u FILE:payload.bin TCP:"PS4 IP":9020
you can then trim out the socket prints or you can adapt it with 2 sockets, one for dumping, another for logging.
To compile for 5.05 you need to use an *** with changes for 5.05 support, i have used https://github.com/xvortex/ps4-payload-***
PS4 5.05 Jailbreak by seanp2500
PS4 5.05 Jailbreak Tutorial by MODDED_WARFARE
5.05 Installing Package Files (PS4/PS2 Games & Custom Themes) by MODDED_WARFARE
5.05 Kernel Exploit Full Tutorial by Andrew Marques
PS4 Pr0 5.05 Debug Menu by GrimDoe
PS4 Pr0 5.05 / PS2 (Mortal Kombat - Armageddon) by GrimDoe
How to Jailbreak PS4 5.05 Jailbreak Tutorial
A few notes on the 5.05 exploit:
1) The page will crash after the kernel exploit successfully runs, this is normal
2) First load after successful exploitation will autoload HEN and Mira (can get klog by nc [ps4 ip] 9998
3) Subsequent loads go to the usual payload launcher.
This is for those who don't like reading manuals, or simply can't read.
IP: 13.37.13.37
AP: ESP8266XploitHost
AP Password: ps4xploit (you can change it from the tools menu)
FTP user: ps4xploit
FTP password: ps4xploit (if you change the AP pass, this one will change too,)
Port: 21
PS4 Fan Speed for 5.05 Kernel thanks to TheoryWrong:
Code:
All here is for 5.05 Kernel:
```int status = icc_query(void* msg_in, void* msg_out);```
icc_query: 0x43540
Sony like to use msg_in addr to message out
Size of habitual message: 0x7F0 (2032 bytes) (use bzero and the stack but i think you can use calloc)
Possible thermal get message:
```
| By the code | Inside the kernel memory
[00 09 10 00 00 00 00 1A 00 00] [00 00 00 00 00 80 00 00 80 00 00 85]
```
i doesn't have check the return (SceIccThermal on kernel)
Some other possible message is in the function of this function function <= yeah i know :') => 0xA83D0
Possible buzzer:
```
| By the code
[00 09 00 00 00 00 00 00 00 20]
```
Possible get fan message:
```
| By the code
[00 0A 05 00 00 00 00 00 00 20]
```
msg_out => `int* rpm_speed = (int*)return_buffer+0xE;`
(Note: The PS4 have 2 thermal captor GPU / CPU) you can get one with the acpi)
ACPI PART for the captor 2 :
```
devclass_get_device: 0x312600
device_get_softc: 0x312650
acpi_tz_get_temperature: 0xD670
devclass_find: 0x312020
```
See: https://github.com/freebsd/freebsd/blob/master/sys/dev/acpica/acpi_thermal.c
you need to add this in a header
```
#define TZ_ZEROC 2731
#define TZ_KELVTOC(x) (((x) - TZ_ZEROC) / 10), abs(((x) - TZ_ZEROC) % 10)
struct acpi_tz_softc {
device_t tz_dev;
ACPI_HANDLE tz_handle; /*Thermal zone handle*/
int tz_temperature; /*Current temperature*/
int tz_active; /*Current active cooling*/
#define TZ_ACTIVE_NONE -1
#define TZ_ACTIVE_UNKNOWN -2
int tz_requested; /*Minimum active cooling*/
int tz_thflags; /*Current temp-related flags*/
#define TZ_THFLAG_NONE 0
#define TZ_THFLAG_PSV (1<<0)
#define TZ_THFLAG_HOT (1<<2)
#define TZ_THFLAG_CRT (1<<3)
int tz_flags;
#define TZ_FLAG_NO_SCP (1<<0) /*No _SCP method*/
#define TZ_FLAG_GETPROFILE (1<<1) /*Get power_profile in timeout*/
#define TZ_FLAG_GETSETTINGS (1<<2) /*Get devs/setpoints*/
struct timespec tz_cooling_started;
/*Current cooling starting time*/
struct sysctl_ctx_list tz_sysctl_ctx;
struct sysctl_oid *tz_sysctl_tree;
eventhandler_tag tz_event;
struct acpi_tz_zone tz_zone; /*Thermal zone parameters*/
int tz_validchecks;
int tz_insane_tmp_notified;
/* passive cooling */
struct proc *tz_cooling_proc;
int tz_cooling_proc_running;
int tz_cooling_enabled;
int tz_cooling_active;
int tz_cooling_updated;
int tz_cooling_saved_freq;
};
```
and add this header from freebsd-header:
```
#include <sys/param.h>
#include <sys/bus.h>
```
Function declaration:
device_t devclass_get_device(devclass_t dc, int unit);
void* device_get_softc(device_t dev); Note: don't forget to cast it to a struct acpi_tz_softc* !
static int acpi_tz_get_temperature(struct acpi_tz_softc *sc);
devclass_t devclass_find(const char *classname);
you need to get the devclass_t of acpi_tz
pseudo code:
```
struct acpi_tz_softc *sc;
device_t *devs;
int devcount, i;
devclass_t thl = devclass_find("acpi_thermal");
devclass_get_devices(thl, &devs, &devcount);
for (i = 0; i < devcount; i++) {
sc = device_get_softc(devs[i]);
if (!acpi_tz_get_temperature(sc)) {
// Do something with TZ_KELVTOC(sc->tz_temperature) (it's a double int, int . int => 23 . 55 C° for example)
}
}
```Download: 505_fself.bin (1.32 MB)

