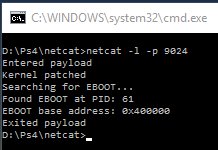
Continuing in the holiday rush since the 4.05 PS4 Kernel Exploit release, we've now seen a 4.05 Kernel Dump and Rizzo Signatures for 4.05 surface alongside some code (below) that scene developers can use for a payload to kick off PS4 4.05 game modding from Skillsofcape (aka @01cedric) following his work on the WEBRTM Game Mod Project. 
Next up, since the PS4 Fat, Slim and Pro Serial / Flash Pinouts were documented PlayStation 4 scene developer VVildCard777 turned up the heat after his PS4 Debug Settings Demo by sharing some UART Enabler 4.05 payload code (below) for developers interested in making use of the PS4 UART for further research.
The PS4 PUP Unpacker also continues getting updated from Zer0xFF, while PlayStation 4 developer @zecoxao announced on Twitter that Zer0Tolerance discovered the method Sony uses for generating "metadata" in lv1 fselfs.
4.05 Kernel
Enjoy Game Modding on 4.05 

proc_rwmem on 4.05 (for payload usage)
Happy Modding 
kern_ptrace on 4.05 (for payload usage)
Happy Modding 
Disable Process ASLR 4.05 (Not tested):
Kernel patch to disable process ASLR on 4.05
uart enabler for 4.05
right, i only solder 1 wire (tx on ps4) and attach gnd wire to hdd cage, then using like 5$ uart to usb i listen on arduino (serial montor). very simple.
Zer0Tolerance found the method Sony uses for generating the "metadata" in lv1 fselfs. Documentation Soon
fun fact: they use a random generator
Download: randtool-master.zip / GIT
From the README.md file: randtool
Implementation of the algo used to generate lv1 fselfs "metadata"
Thanks to @DarkElementPL, @FabOne, @raedoob, @Trojaner and @Wultra for the news tips in the PSXHAX Shoutbox earlier today!

Next up, since the PS4 Fat, Slim and Pro Serial / Flash Pinouts were documented PlayStation 4 scene developer VVildCard777 turned up the heat after his PS4 Debug Settings Demo by sharing some UART Enabler 4.05 payload code (below) for developers interested in making use of the PS4 UART for further research.
The PS4 PUP Unpacker also continues getting updated from Zer0xFF, while PlayStation 4 developer @zecoxao announced on Twitter that Zer0Tolerance discovered the method Sony uses for generating "metadata" in lv1 fselfs.
4.05 Kernel
Code:
proc_rwmem > 0xFFFFFFFF9F0B3BB0proc_rwmem on 4.05 (for payload usage)
Code:
#define KERN_PROC_RWMEM 0x0ABBB0 int(*proc_rwmem)(int addr, int len) = NULL; proc_rwmem = (void *)&ptrKernel[KERN_PROC_RWMEM];kern_ptrace on 4.05 (for payload usage)
Code:
#define KERN_PTRACE 0x0AC230 int(*ptrace)(int req, int pid, void *argsAddr, int data) = NULL; ptrace = (void *)&ptrKernel[KERN_PTRACE];Disable Process ASLR 4.05 (Not tested):
Code:
*(uint16_t *)0xFFFFFFFF9F28E202 = 0x63EB; #define DISBL_PROC_ASLR 0x286202
Code:
*(uint16_t*)(kernelBase + 0x2862D6) = 0x9090;uart enabler for 4.05
Code:
uint16_t *securityFlags = (uint64_t *)(kernel_base+0x2001516); *securityFlags = *securityFlags & ~(1 << 15); *(char *)(kernel_base + 0x186b0a0) = 0;Zer0Tolerance found the method Sony uses for generating the "metadata" in lv1 fselfs. Documentation Soon
fun fact: they use a random generator
Download: randtool-master.zip / GIT
From the README.md file: randtool
Implementation of the algo used to generate lv1 fselfs "metadata"
Thanks to @DarkElementPL, @FabOne, @raedoob, @Trojaner and @Wultra for the news tips in the PSXHAX Shoutbox earlier today!



